Cyber Crimes
In this article, we shall discuss the issue of cyber crimes in international relations. We will answer the question “What is a Cyber Crime,” discuss the different types of cyber crimes committed, as well as how governments, nongovernmental organizations, as well as and international organizations are doing to combat cyber crimes. The article will end with a list of scholarly books on the issue of cyber crimes, as well as a list of references.
What is Cyber Crime?
While there are various definitions and categories of cyber crimes, “cyber crimes are standard crimes committed online or harmful behavior that is connected to computers. Examples of cybercrimes are fraud, pornography, smuggling, copyright and software piracy, identity theft, and extortion” (Payne, 2013: 267). Related to this issue of cyber crime, the internet, and computers, Beal (2014) says about cyber crimes that “Cyber crime encompasses any criminal act dealing with computers and networks (called hacking). Additionally, cyber crime also includes traditional crimes conducted through the Internet. For example; hate crimes, telemarketing and Internet fraud, identity theft, and credit card account thefts are considered to be cyber crimes when the illegal activities are committed through the use of a computer and the Internet.” Thus, cyber crimes are very similar to “traditional crime”, but the difference is that it is carried out through the internet, affecting many individuals, “as well as unauthorized access, damage and interference to computer systems” (Broadhurst, 2006: 2). Also, many a cyber crime may fall under the category of a transnational crime if it extends across multiple state borders.
However, many states still do not make the distinction between cyber crimes and other sorts of crimes. For example, as Kristin M. Finklea and Catherine A. Theohary (2013) explain when speaking about the United States with regards to cyber crime, they state that:
“The U.S. government does not appear to have an official definition of cybercrime that distinguishes it from crimes committed in what is considered the real world. Similarly, there is not a definition of cybercrime that distinguishes it from other forms of cyber threats, and the term is often used interchangeably with other Internet- or technology-linked malicious acts. Federal law enforcement agencies often define cybercrime based on their jurisdiction and the crimes they are charged with investigating. And, just as there is no overarching definition for cybercrime.”
What are the Different Types of Cyber Crimes Committed?
The rise of the internet and increased globalization has made it easier for individuals to commit crimes, and many of them cyber crimes. There are many ways that they commit such crimes. For example, online shopping and online shopping websites has been one of the most frequent ways that cyber crimes are committed. Cyber criminals have attempted to scam people from their money through shopping platforms. For example, they may try to hack a site and steal personal information, and within this credit card information, that they then use; this direct stealing is a serious issue, and police and credit card companies have devoted great resources to stopping such illegal cyber crimes. Along with stealing information, large shopping sites are used by individuals to commit many other crimes. For example, Richard Payne (2013) explains this when discussing the auction site Ebay. Speaking of Ebay, he explains that “the biggest online marketplace, has roughly 180 million members worldwide, who are connected to the Internet, and more than 60 million items for sale at any particular moment. Both distance and anonymity conspire to render these global online shopping centers perfect places for fraudulent activities. As a marketplace that links buyers and sellers, eBay has very little control over transactions” (267). Related to this point, it is very difficult for such companies to monitor all activity that is taking place.
Other individuals have used the internet to commit cyber crimes such as stealing software. This issue of cyber piracy is a cyber crime that goes against the right of intellectual property (Payne, 2013). Regarding online piracy as it relates to music and movies, the issue here is that while illegal, scholars and others have argued that the piracy of software has become so commonplace “that many ordinary individuals do not perceive stealing software as a crime, thereby further blurring the boundaries between legal and illegal behavior” (Payne, 2013: 267). This is happening throughout much of the world, although much of the software activities are taking place in Global North states, as well as rising economic states such as China (Payne, 2013), whereas music and films are also happening on a global scale.
Email Cyber Crimes
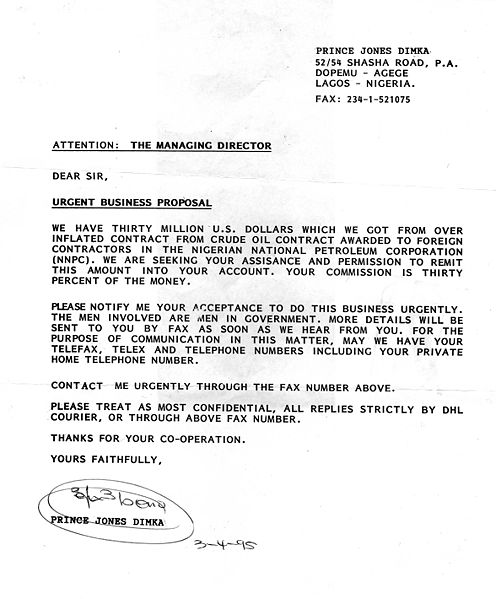
Individuals are also using electronic communication to carry out cyber crimes against individuals. Individuals have tried to scam individuals of money through communication. For example, one of the most often-occured types of email or electronic communication cyber crimes is known as “The Nigerian scam” or “advance fee fraud scams” (Park, Jones, McCoy, Shi, & Jakobson (2014). This type of cyber crime involves an individual “send[ing] an e-mail asking prospective victims to assist him or her to transfer millions of recently acquired dollars out of Nigeria in exchange for a substantial part of the money. Prospective victims are instructed to deposit their own money into a specified bank account to demonstrate their honesty and willingness to cooperate. If these instructions are followed, the money and the Nigerian e-mail sender simply vanish” (Payne, 2013: 268).
These sorts of scams, while popular with this pitch, have developed in other manifestations. One of the more recent types of advance fee fraud scams is one that is carried out on Craigslist (Park, Jones, McCoy, Shi & Jakobson, 2014), and have often involved the sale of cars. Garg & Nilizadeh (2013) explain a type of scam on Craigslist when they say:
“Craigslist automobile scams are a typical instantiation of advance fee frauds. A possible scam in Craigslist’s automobile section would include a scammer who posts lucrative advertisements for automobiles. The quoted price for such vehicles is irrationally low; arguably setting an unrealistically low price allows the scammer to filter out the individuals that are unlikely to be adequately gullible. Despite the extant signal of an irrationally low price the scammer would receive responses from potential victims. The scammers would then attempt to con these individuals with stories that would explain the reason for the unreasonably low price. For example, the seller might pretend to be an international traveller who inexplicably has to move back to his or her home country on short notice. Transactions are carried out using third-party agents, such as BidPay, Squaretrade, or PayPal. Victims advance the money to the scammers without getting the vehicle in return” (124).
Politically Motivated Cyber Crimes
Along with financial cyber crimes, there have also been politically motivated cyber crimes that have taken place. Many states are worried about the threat of hackers being able to enter into their computer systems and threatening state security. There have been concerns that countries such as Russia and China have wanted US intelligence with regards to military information (Payne, 2013). There are also groups that have tried to use computer viruses to reach their political objectives. For example, “[a]n Internet virus named Kama Sutra–named after the venerable Indian guide to eroticism–was programmed to overwrite documents, images, and compressed computer filed” (268). Criminal organizations have used carried out such cyber crimes with the intention of stealing critical information such as passwords (Payne, 2013).
One of the most controversial groups in recent memory with regards to cyber crimes has been the group Anonymous, which is a group of individuals carrying out various cyber activities under this group, but who do not share their identity. However, due to its security, it is difficult to define the group. And “[w]hile scholars, theorists, law enforcement, and policymakers may not always agree on how to conceptualize or categorize the Anonymous entity, it is generally agreed that it operates with two broad tenets: (1) personal anonymity and (2) the free flow of information.55 Anonymous is a loosely formed organization to the extent that it cannot be easily categorized” (Finklea & Theohary, 2013: 12). The reason is that while some see it as a criminal group breaking various privacy and security laws by committing cyber crimes, others see individuals who are doing this for the sake of human rights and social justice activism (Finklea & Theohary, 2013).
Government Responses to Cyber Crimes
Governments have a tough time with cyber crimes. Part of the reason is that with the evolving technology, and the quick continued rise of globalization, it is becoming very difficult to eliminate all of the ways that cyber crimes are being committed. Furthermore, some countries do not have set approaches specifically for cyber crimes, but instead treat it the same as other criminal activity. In fact, some have wondered what approach is best to fight cyber crime, to treat it as its own category, or as other crimes, and thus, using similar approaches that one would use against other forms of criminal activity. In fact, many in the United States have asked such a question (Finklea & Theohary, 2013).
Scholarly Books on Cyber Crimes
P.W. Singer & Allan Friedman, Cybersecurity and Cyberwar: What Everyone Needs to Know
Marjie T. Britz, Computer Forensics and Cyber Crime: An Introduction
References
Beal, V. (2014). What is a Cyber Crime. Webopedia. Available Online: http://www.webopedia.com/TERM/C/cyber_crime.html
Broadhurst, R. (2006). Developments in the Global Law Enforcement of Cyber-Crime. An International Journal of Police Strategies and Management, Vol. 29, No. 2, pages 408-433.
Garg, V. & Nilizadeh, S. (2013). Craiglist Scams and Community Composition: Investigating Online Fraud Victimization. 2013 IEEE Security and Privacy Workshops, pages 123-126. Available Onlhttp://www.ieee-security.org/TC/SPW2013/papers/data/5017a123.pdf
Finklea, K.M., & Theohary, C.A. (2013). Cybercrime: Conceptual Issues for Congress and U.S. Law Enforcement, pages 1-26. January 9, 2013. Available Online: http://fas.org/sgp/crs/misc/R42547.pdf
Park, Y., Jones, J., McCoy, D., Shi, E., & Jakobson, M. (2014). Scambaiter: Understanding Targeted Nigerian Scams on Craigslist. Available Online: https://www.cs.umd.edu/~elaine/docs/scambaiter.pdf
Payne, R. (2013). Global Issues. New York, New York. Pearson.